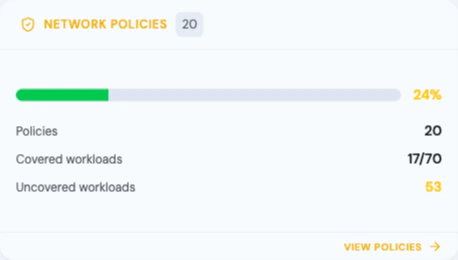
Network Policies control pod-to-pod and pod-to-external traffic at the network level. Radar supports standard Kubernetes NetworkPolicy as well as Cilium’s CiliumNetworkPolicy and CiliumClusterwideNetworkPolicy CRDs, providing visibility into what traffic is allowed, denied, and which workloads are unprotected.Documentation Index
Fetch the complete documentation index at: https://radarhq.io/docs/llms.txt
Use this file to discover all available pages before exploring further.
What Radar Shows
Topology: NetworkPolicy and CiliumNetworkPolicy nodes appear in the topology graph with edges connecting them to the workloads they protect. See at a glance which deployments have network policies applied and which are exposed.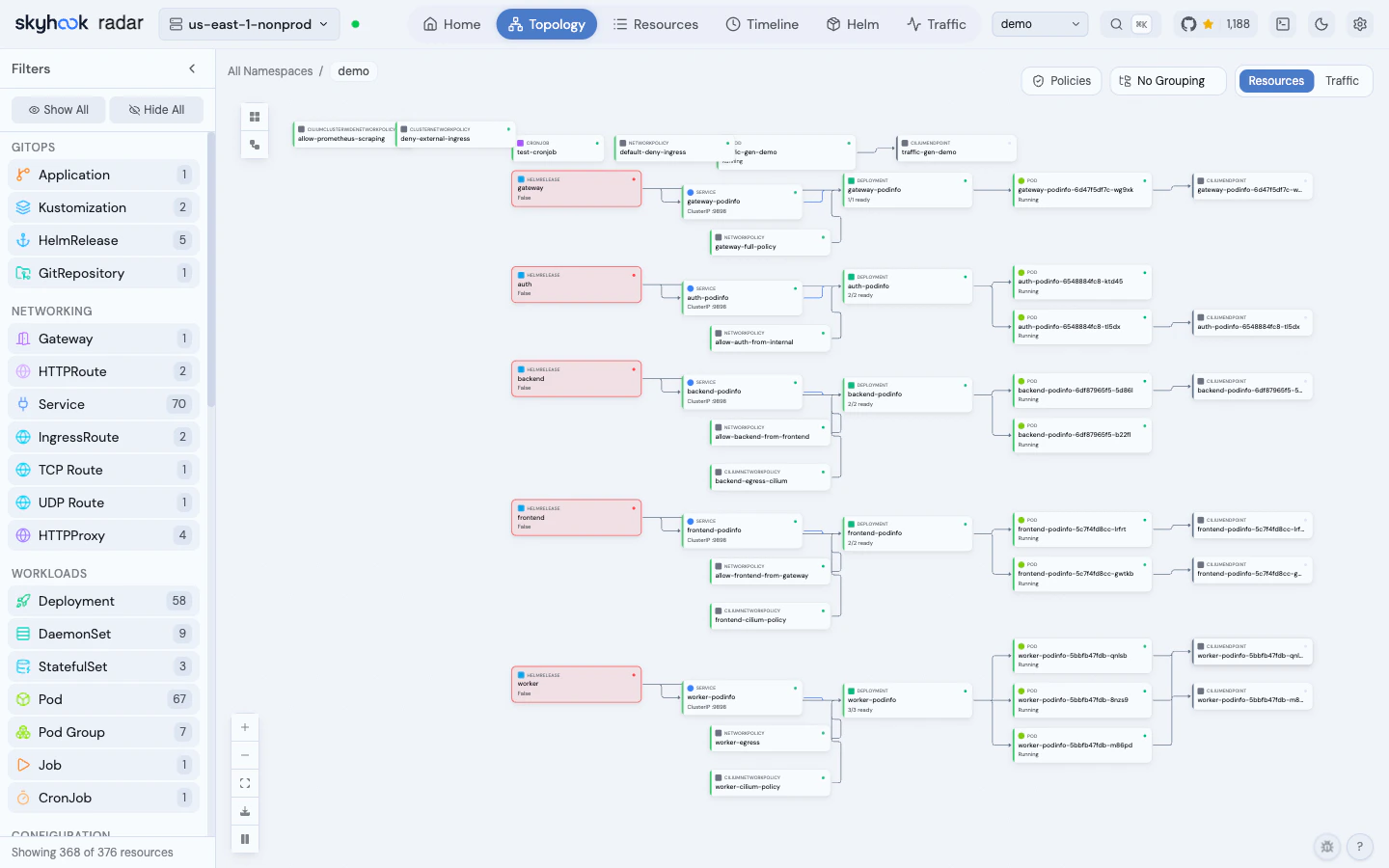
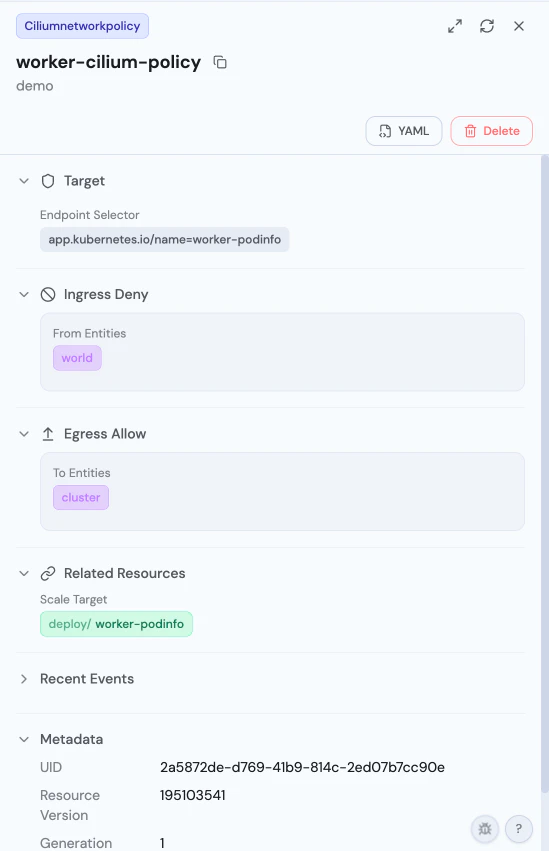
- Endpoint selector targeting
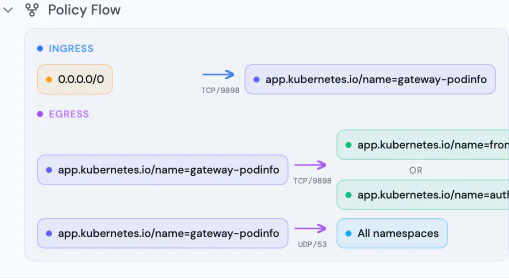
- Ingress/egress rules with allow and deny semantics
- Cilium-specific entity selectors (world, cluster, host)
- CIDR rules, port/protocol specifications
- Related workloads with clickable links
- Pod selector and namespace selector rules
- Ingress and egress rules with CIDR blocks, ports, and protocols
- Policy type indicators (Ingress, Egress, or both)
- Related resources showing protected workloads

Supported Resources
| Resource | Group | Topology | Detail View | AI Summary |
|---|---|---|---|---|
| NetworkPolicy | networking.k8s.io/v1 | Yes | Yes | Yes |
| CiliumNetworkPolicy | cilium.io/v2 | Yes | Yes | Yes |
| CiliumClusterwideNetworkPolicy | cilium.io/v2 | Yes | Yes | Yes |