Inspect container contents without kubectl exec.
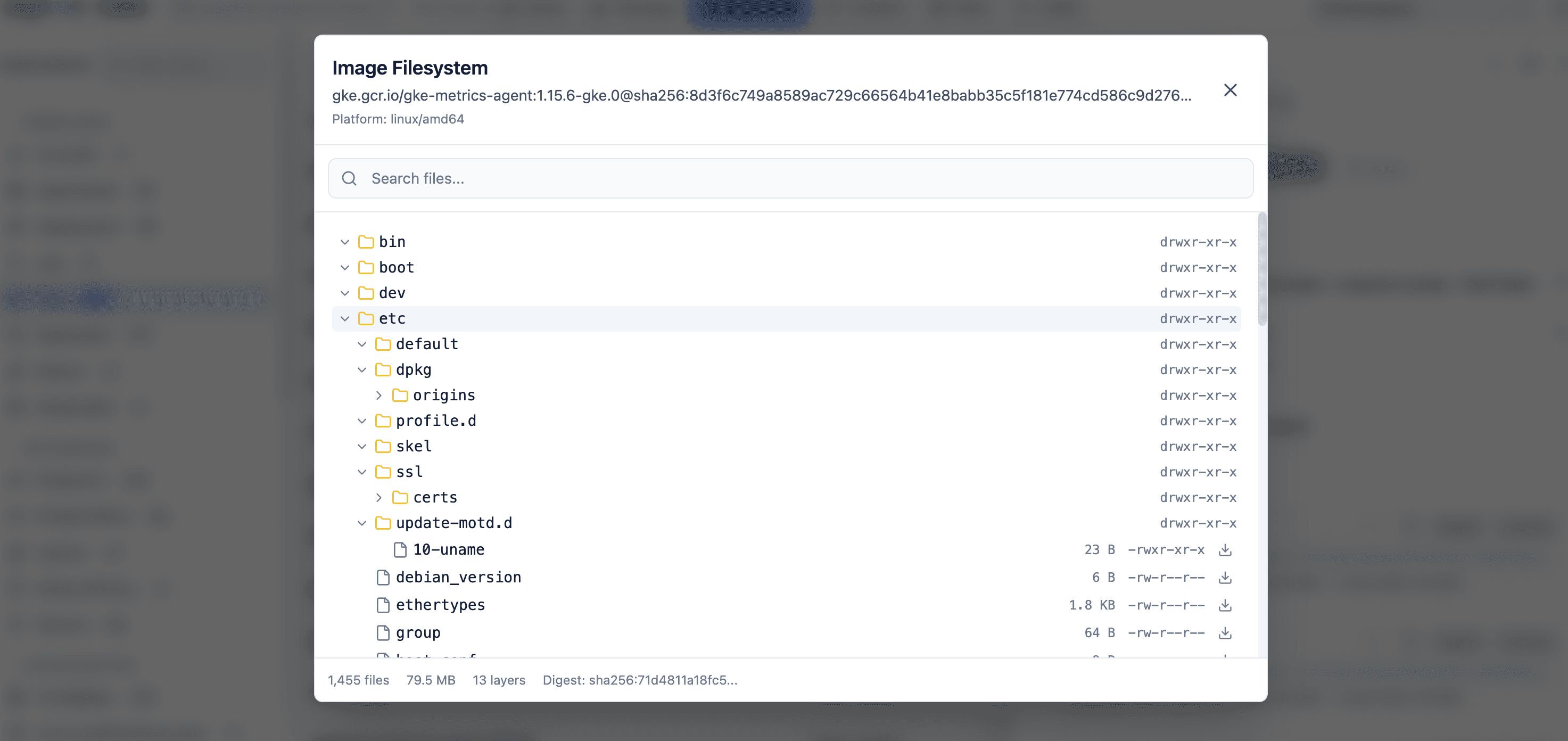
Click any container in a Pod view and browse its full filesystem - tree, sizes, symlinks, search, download. No docker pull, no exec, no local daemon. Private registries included.
“What actually shipped in this image?”
You're debugging a flaky deployment. The image tag is v2.4.0-rc3. You think it has a specific binary at /app/bin. You don't remember if the Dockerfile actually put it there.
Option A: kubectl exec -it pod -- ls /app/bin. That assumes the pod is still running. It assumes the container has ls installed. It assumes your distroless image has a shell, which it doesn't.
Option B: docker pull ... && docker run ... on your laptop. Now you need docker installed, you need the image-pull credentials the cluster uses (the ones you don't have on your laptop), and you're running a random container locally to answer a question about a remote one.
Radar's Image Filesystem Viewer skips both. It pulls the image layers directly from the registry using the cluster's own ImagePullSecrets, extracts them to a local cache, and shows you the filesystem in a tree. No docker. No exec. No shell in the image.
Six things the viewer handles.
Full filesystem tree with sizes
Browse the image like a local directory. File sizes, permissions, symlinks - all rendered in a tree view with expandable directories. Discover what shipped without running the container.
Search across the entire image
Find every file matching a pattern across all layers. Useful when you're asking “does this image have a compiled binary at /app?” and don't want to shell in to find out.
Download individual files
Grab one file from the image without pulling the whole thing. Debug a bad config baked into a build, inspect a vendored binary, extract an embedded asset.
Private registries via ImagePullSecrets
Works with Docker Hub, Quay, GitHub Container Registry, GCR, ECR, and ACR. Radar reuses the cluster's existing ImagePullSecrets - no separate auth config to wire up.
Disk-based layer caching
First browse pulls and extracts layers to a local cache. Second browse of the same image starts in milliseconds. Doesn't re-download, doesn't re-decompress.
One click from any Pod
The viewer lives inside the Pod detail view. Click a container, click Image Filesystem, you're in. No separate tool to open, no docker daemon required, no mental context switch.
Four moments you'll actually use this.
Debug a distroless image
Distroless has no shell. `kubectl exec` returns exit 126. Radar shows you the filesystem anyway - because it doesn't need a shell in the image.
Confirm what CI actually built
The Dockerfile says `COPY dist /app`. Does the image really have `/app/index.html`? One click, find out, without pulling 2GB to your laptop.
Extract a config the app is using
Service reads config from `/etc/myapp.yaml`. That file is baked into the image, not mounted. Download it from the Radar UI, diff against your expected config, done.
Investigate a CVE
Security team says: “the patched binary should be at /usr/bin/openssl, version 3.0.14.” Open the image, navigate to `/usr/bin/openssl`, check the size. Takes ten seconds.
How it actually works.
Registry pull, not docker
Radar talks the OCI distribution spec directly. No docker daemon, no containerd, no local runtime. Works on laptops without docker installed.
Reuses cluster secrets
Radar reads the Pod's ImagePullSecrets, passes them to the registry client, and pulls authenticated. Your private-registry access doesn't need to be replicated on your machine.
Cached by digest
Layer cache is keyed on digest. Two pods running the same image share the cache. Re-opening the viewer is instantaneous; the second engineer on the same image pays no download cost.
Apache 2.0. Yours to inspect, fork, or self-host.
Radar's source is on GitHub. Every feature on this page is in the binary you install with brew install. No telemetry, no mandatory login, no phone-home. If we ever change that, you'll see it in a diff first.
Four more things Radar does in the same binary.
Live topology graph
Every resource and connection, laid out by ELK.js, updated via SSE.
Event timeline
Every K8s event and resource change, retained past the 1-hour TTL.
Cluster audit
31 best-practice checks across security, reliability, and efficiency.
AI via MCP
Give Claude, Cursor, or Copilot a safe, token-optimized view of your cluster.
The feature that makes people install Radar and not uninstall.
Once you've browsed an image tree without kubectl exec, you won't want to do it any other way.
Apache 2.0 OSS · Unlimited clusters self-hosted · Hosted free tier for up to 3 clusters